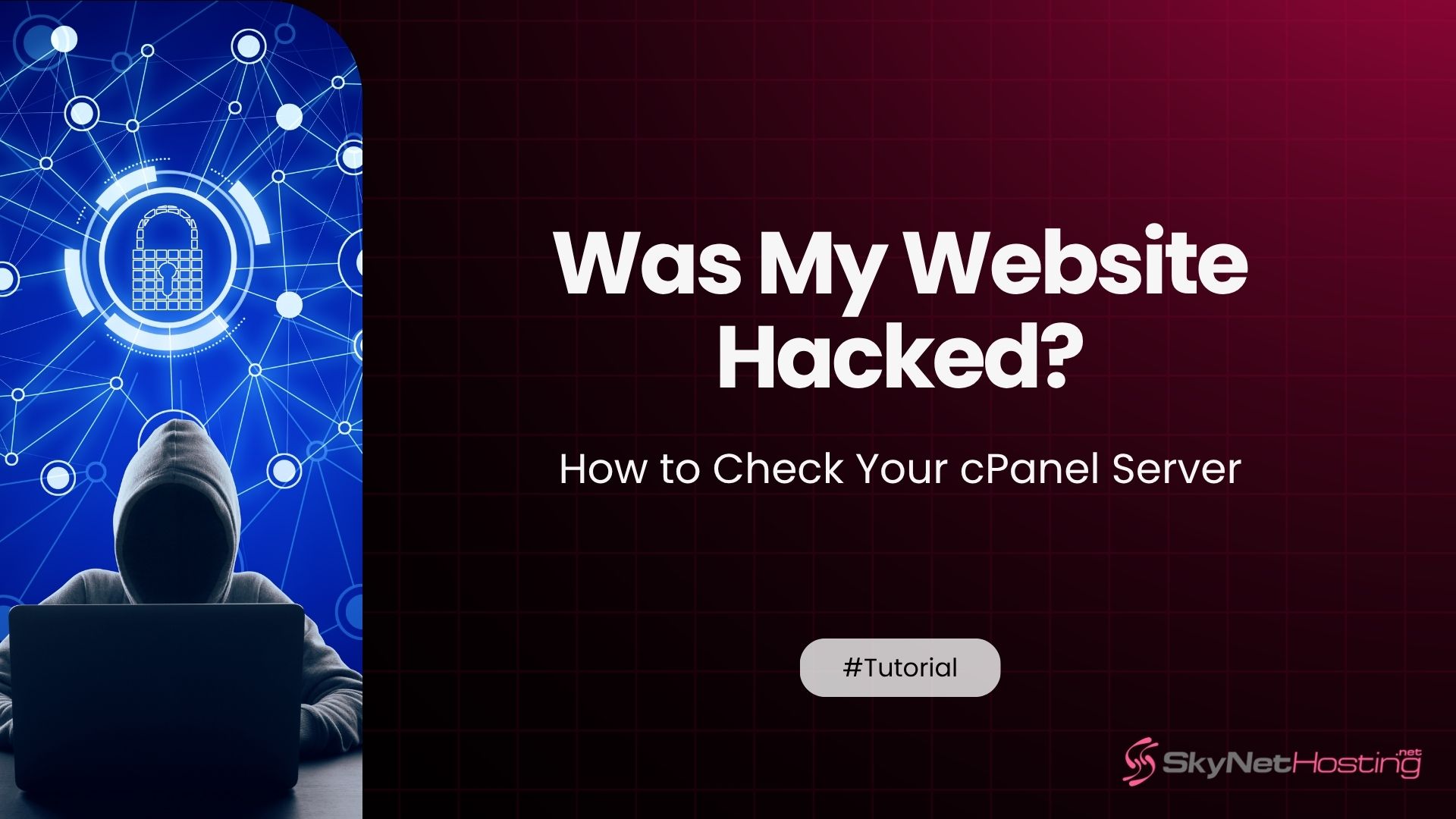
Was your website hacked via CVE-2026-41940? How to check your cPanel server
TL;DR
- Hack Impact: CVE-2026-41940 gave root access via CRLF session injection, compromising entire servers (not just sites), with 65-day exploit window from Feb-Apr 2026.
- Warning Signs: Look for unexpected files in public_html, rogue DB tables, spam emails, redirects, unknown accounts, CPU spikes, defacements, new FTP/SSH/cron jobs.
- Session Checks: Inspect /var/cpanel/sessions/raw/ for forged root sessions (user=root, hasroot=1, tfa_verified=1); run cPanel IOC script ioc_checksessions_files.sh.
- Log Audits: Review /usr/local/cpanel/logs/access_log, /var/log/wtmp (via
last), Apache for eval() POSTs; focus on Feb 23-Apr 28 activity. - Backdoor Hunt: Revoke API tokens, check ~/.ssh/authorized_keys, cron jobs, webshells in PHP files, nuclear.x86/XMRig miners.
- Recovery Steps: Purge sessions, reset all creds, malware scan (Imunify360/ClamAV), consider full rebuild; harden with 2FA, CSF firewall, VPN.
If you use cPanel, you are not alone. In my 20 years of managing servers, I have seen many attacks. But the recent cPanel CVE-2026-41940 compromise is one of the worst. It left thousands of servers wide open. Hackers found a way in, and they did not even need a password.
In this guide, I will show you exactly how to check if a cPanel server is compromised. We will look at the warning signs, check your logs, and hunt down hidden malware. Let us find out if your server is safe, and what to do if it is not.
For a detailed overview of the issue and its implications, check out our main blog, cPanel Hack 2026: CVE-2026-41940 Zero-Day Nightmare – 70M Domains at Risk, which dives deeper into this critical vulnerability and how it affects millions of domains worldwide.
What Does It Mean When Your cPanel Server Gets Hacked?
A hacked cPanel server is a nightmare. It means attackers have full control over your web hosting environment. They can see your files, read your emails, and access your databases.
CVE-2026-41940 and How Hackers Got Root Access Without a Password
In early 2026, a massive zero-day exploit hit the web. We call it CVE-2026-41940. It is a critical cPanel authentication bypass vulnerability. Attackers used a trick called CRLF injection on cPanel session files.
Basically, they forged a fake session file. They told the server they were the “root” user. The server believed them. Just like that, hackers bypassed the login screen. You can read more about the technical details on the official CVE record.
Why cPanel Compromises Are More Dangerous Than Ordinary Website Hacks
An ordinary website hack usually affects one site. Maybe a hacker guesses your WordPress admin password. But a cPanel server hacked at the root level is different.
If someone gets root access through WHM, they own the entire server. If you run a web design business, your reseller hosting security is gone. Every single website on that server is compromised.
What Attackers Can Do Once Inside Your Server
Once they get inside, hackers act fast. They often install the nuclear.x86 malware cPanel users have been reporting. They might set up an XMRig crypto miner to steal your server power.
They also steal data. They copy your customer lists, passwords, and emails. Sometimes, they use your server resource spike to send millions of spam emails.
The 65-Day Exploitation Window and Why Your Server May Already Be Compromised
The scary part? Attackers knew about this flaw long before a patch existed. There was a 65-day exploitation window.
From late February to late April 2026, servers were completely vulnerable. Even if you patched your server the day the update came out, hackers might have already left a backdoor.
What Are the Warning Signs That Your cPanel Was Hacked?
How do you know if someone got in? Hackers try to hide, but they always leave footprints. Here are the hacked cPanel server signs you need to look for.
Unexpected File Changes in public_html and Core Directories
The first place to look is your public_html folder. Look for files you did not create. Public_html malicious file detection is vital. If you see weird PHP files with random letters for names, you have a problem.
Unusual Database Activity and Rogue Tables in MySQL
Hackers love databases. They store all the valuable data. Check your MySQL databases for unauthorized changes. You might find new users or rogue tables that do not belong to your applications.
Server Sending Spam or Unexpected Bulk Emails
Is your server suddenly slow? Are legitimate emails bouncing back? This is a huge cPanel email spam indicator. Hackers often turn compromised servers into spam factories.
Unexplained Website Redirects to Malicious URLs
You type in your domain name. But instead of your homepage, you land on a strange ad site. Website redirect malware cPanel attacks are very common. Hackers alter your core files to steal your traffic.
New Unknown User Accounts in WHM or cPanel
Log into WHM and check your account list. Look for a WHM account list unauthorized entry. If you see a cPanel user you did not create, a hacker made it. They use these fake accounts to keep access to your server.
Sudden Server CPU or Memory Spikes With No Explanation
Keep an eye on your server load. An XMRig crypto miner cPanel server infection will max out your CPU. If your server resource spike happens every night at 2 AM, someone is using your machine.
Website Defacement or Content Changes You Did Not Make
Sometimes hackers want to show off. Website defacement detection is easy. They change your homepage to display their hacker group logo. If your site looks totally different, you have been hacked.
Unauthorized FTP Accounts, SSH Keys, or Email Forwarders
Hackers need ways to get back in later. They create an email forwarder backdoor cPanel trick to steal password reset links. You should also do a quick FTP account audit cPanel check.
Suspicious Cron Jobs Running in the Background
Cron jobs are automated tasks. Hackers use a cron job backdoor cPanel trick to run malware every few minutes. Check the cron jobs for every user on the server. Look for weird commands downloading external files.
How Do You Check cPanel Session Files for Signs of Compromise?
If you suspect a cPanel CVE-2026-41940 compromise, you must check the session files. This is where the hackers broke in.
The /var/cpanel/sessions/raw/ Directory and Why It Is the First Place to Look
When you log into cPanel, it creates a session file. These live in the /var/cpanel/sessions/raw/ folder. Since the attackers used CRLF injection session file tricks, we need to inspect this directory. You can learn more about how cPanel manages sessions on the cPanel documentation site.
Forged Session File Indicators — user=root, hasroot=1, and tfa_verified=1
Hackers faked their identity. You need to look for cPanel session files suspicious entries. Look inside the raw files.
If you see a user=root session forgery, that is bad. Also look for hasroot session injection. The most obvious sign is a cPanel tfa_verified bypass detection. This means they skipped your two-factor authentication.
Understanding the successful_internal_auth_with_timestamp Flag
Another major red flag is the successful_internal_auth_with_timestamp string. Attackers injected this to trick the server into thinking an admin had already approved the login.
Running the Official cPanel IOC Detection Script Step by Step
cPanel released a script to help you check. The cPanel IOC detection script looks for these bad session files. You can find the script and instructions on the official cPanel support article. You run it via SSH as the root user.
Using the watchTowr Detection Artifact Generator Script
Security researchers also made tools. The watchTowr Detection Artifact Generator is a great open-source tool. It scans your server for signs of the exploit. You can find similar community tools on GitHub.
Understanding CRITICAL vs WARNING Results From the Detection Script
When you run the script, it prints results. A WARNING means it found something strange, but it might just be a glitch. A CRITICAL result means the script found hard evidence of an attack. Take CRITICAL alerts very seriously.
How Do You Audit cPanel Access Logs to Find Evidence of a Breach?
Logs tell the story of what happened on your server. Let us do some cPanel access log forensics.
Log Files to Check First After Suspecting a Compromise
Start with the basics. Check /usr/local/cpanel/logs/access_log. This shows every time someone tries to log into cPanel or WHM.
Reading WHM Access Logs for Unauthorized Login Attempts
Look for WHM unauthorized access. If you see successful logins from IP addresses in countries you do not live in, that is a huge red flag. Look out for cPanel brute force login attempts as well.
Checking /var/log/wtmp for Suspicious IP Addresses
The /var/log/wtmp file tracks SSH logins. A quick post-compromise cPanel cleanup step is running the last command. This reads the wtmp file. Do a cPanel /var/log/wtmp audit to see who accessed your server terminal.
Identifying Malicious POST Requests and eval() Calls in Apache Logs
Hackers interact with malware through the web. Check your Apache logs. Look for strange POST requests to weird files. If you see eval() commands in the URL, someone is trying to run malicious code.
The Critical Time Window — February 23 to April 28 2026
When looking through logs, focus on the gap between February 23 and April 28. This is the zero-day exploit cPanel 2026 timeline. The KnownHost exploitation February 2026 incident showed that hackers were highly active during this period.
Spotting Malicious Redirects and PHP Injections in .htaccess Files
The .htaccess file controls how your website loads. Hackers alter it to create malicious redirects. Check this file in every single website directory. If you see weird rewrite rules pointing to off-site domains, fix it immediately.
How Do You Find Backdoors and Persistent Access Left by Hackers?
Hackers do not want to lose access. They leave backdoors behind. You have to find and close them all.
Auditing API Tokens in WHM for Unauthorized Keys
WHM lets you create API tokens. Hackers use a cPanel API token backdoor to control your server remotely. Log into WHM and check the API tokens page. Delete any tokens you do not recognize.
Checking SSH Authorized Keys for Rogue Entries
A cPanel SSH key audit is critical. Hackers add their own SSH keys to your server. This lets them log in without a password. Check the ~/.ssh/authorized_keys file for every user, especially the root user.
Scanning Cron Jobs for Hidden Malware Commands
I mentioned cron jobs earlier, but it is worth repeating. Use the command line to list cron jobs for all users. Look closely at anything downloading files using curl or wget.
Detecting Web Shells in public_html PHP Files
A web shell gives a hacker a secret control panel on your website. Webshell detection cPanel scans are vital. They often hide in files named db.php or config.php.
Checking WordPress wp_users and wp_options Tables for Rogue Admins
If you run WordPress, hackers will target it. They inject a wp_users rogue admin account. Check your database tables. Make sure you recognize every admin user. For extra safety, follow a solid WordPress security on shared hosting guide.
Identifying the nuclear.x86 Botnet and XMRig Crypto Miner on Your Server
These are the most common payloads right now. The nuclear.x86 malware cPanel infection connects your server to a botnet. You can usually find these running in the background using the top command in SSH.
How Do You Run a Full Malware Scan on a Compromised cPanel Server?
You need automated tools to help you find all the hidden files. A cPanel malware scan is mandatory.
Using Imunify360 to Scan for Malware on cPanel
Imunify360 is an amazing tool. Many hosting companies include it. An Imunify360 malware scan cPanel run will detect almost everything. It automatically cleans infected files and blocks bad IPs.
Running ClamAV on a cPanel Server via SSH
If you do not have Imunify360, use ClamAV. It is free. A ClamAV server scan will catch a lot of common malware. You can install it through WHM and run it from the command line. Ask for advice on Reddit’s cPanel community if you need help configuring it.
Using the GitHub cPanel Compromise Detection Script
The security community built great scripts. You can download the GitHub detection script specifically for this vulnerability. It checks your logs, sessions, and common malware paths in one go. You can find discussions on how to use it safely in various security forums.
Next Steps When a Malware Scanner Returns Positive Results
If the scanner finds malware, do not panic. Quarantine the files first. Do not just delete them, as it might break your website. Review the files to understand what they do.
What Should You Do Immediately After Confirming Your cPanel Was Hacked?
If you confirm a breach, you must act fast. Here is your emergency checklist.
Step 1 — Take the Server Offline and Block All External Access
Stop the bleeding. Disconnect the server from the internet or block all web traffic using your firewall. This stops the hackers from doing more damage while you investigate.
Step 2 — Purge All Sessions in /var/cpanel/sessions/raw/ and /cache/
Kill their active access. Delete all files in the session directories. This forces everyone, including the hackers, to log out immediately.
Step 3 — Reset Root, WHM, cPanel, FTP, Database, and SSH Credentials
Change every single password. This includes root, WHM, cPanel accounts, databases, and FTP. Use long, complex passwords.
Step 4 — Revoke and Regenerate All API Tokens
As we discussed, API tokens are backdoors. Delete all existing tokens. Generate new ones only for the services that absolutely need them.
Step 5 — Remove All Unauthorized Accounts and Cron Jobs
Delete any users or cron jobs you did not create. Check the WHM root access unauthorized logs again just to be sure.
Step 6 — Run a Full Server Malware Scan
Now that you have locked the doors, run your malware scans again. Ensure the server is completely clean.
Step 7 — Targeted Cleanup vs Full Server Rebuild — How to Decide
Sometimes, cleaning up is not enough. If the hackers got root access, you can never truly trust the server again. The safest option is to do a full server rebuild. Install a fresh OS, install a clean cPanel, and restore from a safe backup. Make sure you do a cPanel backup before cleanup just in case.
For detailed instructions on addressing specific vulnerabilities, refer to our blog How to Update cPanel to Fix the CVE-2026-41940 Security Vulnerability (Step-by-Step).
How Do You Find Out If Your Hosting Provider’s Server Was Compromised?
If you use shared hosting, you do not have root access. You have to rely on your provider.
Questions to Ask Your Hosting Provider After the CVE-2026-41940 Incident
Open a support ticket. Ask them directly: “Did you detect a server breach indicators hosting event regarding CVE-2026-41940?” Ask for proof that your specific account is safe. Read more about communicating with hosts in our web hosting issues guide.
Shared Hosting vs VPS vs Dedicated — How the Risk Differs for Each
On shared hosting, the host manages security. On VPS and Dedicated servers, you are responsible. If you need a refresher on the differences, check out this WHM vs cPanel guide.
How Namecheap, KnownHost, InMotion, and HostPapa Protected Their Customers
Top-tier hosts acted quickly. We saw quick hosting provider breach notification emails from many big brands. They force-updated cPanel and ran global malware scans.
Verifying That Your Host Has Patched and Audited Their Servers
Look at your host’s status page. Check their blog. They should have a public statement about the CISA KEV CVE-2026-41940 entry. If your host is silent, that is a bad sign.
How Do You Stop Your cPanel Server From Being Hacked Again?
Once you recover, you need to harden your server. You do not want to go through this again.
Two-Factor Authentication for All WHM and cPanel Accounts
Turn on 2FA for everything. Even if a hacker steals your password, they cannot log in without your phone. This stops 99% of basic attacks.
Restricting WHM Access to Trusted IP Addresses Only
Only allow logins from your home or office IP address. You can configure this easily in WHM under the Host Access Control settings. For more tips on remote safety, see this remote access to VPS guide.
Putting Server Management Behind a VPN Layer
For ultimate security, force admins to connect to a private VPN before they can even reach the WHM login page. It hides your server from the public internet.
Installing and Configuring ConfigServer Security and Firewall
CSF is a free firewall for cPanel. It is incredibly powerful. It blocks bad IPs, prevents brute-force attacks, and alerts you to strange logins. Install it today.
File Integrity Monitoring With AIDE or OSSEC
A cPanel file integrity monitoring system watches your core files. If a hacker alters a system file, AIDE or OSSEC will email you immediately.
Regular Automated Backups to a Remote Location
Never store backups on the same server. If the server burns down, your backups burn with it. Send them to an off-site location like Amazon S3. Do not rely on features that have hidden costs in unlimited hosting.
What Is SkyNetHosting.Net Doing About the cPanel Hack for Its Clients?
If you are a SkyNetHosting.Net client, we have your back. Security is our number one priority.
How SkyNetHosting.Net Detected and Responded to CVE-2026-41940
The moment the CVE was announced, our security team jumped into action. We patched every single server on our network within hours. We ran the official IOC scripts to ensure no client data was breached. You can read our full technical breakdown on fixing CVE-2026-41940.
Current Recovery Progress and What Clients Should Expect
Our shared and reseller hosting comparison networks are 100% secure. If you manage your own unmanaged VPS, we strongly advise you to patch immediately. We have sent emails with step-by-step instructions. If you need help, our support team is ready.
Where to Check the Latest Live Status Updates
We believe in total transparency. Keep an eye on our main blog and network status pages. If you have any concerns about your specific server, open a priority ticket. We will run a manual audit for you.
Staying safe online takes work, but you can do it. Check your logs, run your scans, and always keep your software updated.
FAQs
Was my cPanel server likely hacked in CVE-2026-41940?
Yes, if unpatched between February 23 and April 28, 2026, your server was highly vulnerable to root compromise via session forgery. This zero-day allowed passwordless access, exploited for 65 days before patches, affecting millions of domains with backdoors like nuclear.x86 malware. Run IOC detection immediately to confirm, as signs may linger post-patch.
What are the top warning signs of a cPanel compromise?
Key indicators include unexpected PHP files in public_html, rogue MySQL tables/users, spam outflows, site redirects, unknown WHM/cPanel accounts, CPU/memory spikes from miners, defacements, and suspicious cron jobs/FTP/SSH keys. These stem from root access granting full control over files, DBs, and resources. Audit promptly, as hackers hide traces but leave footprints in logs and directories.
How do I check cPanel session files for CVE-2026-41940 evidence?
Examine /var/cpanel/sessions/raw/ for forged entries like user=root, hasroot=1, tfa_verified=1 without valid origins, or successful_internal_auth_with_timestamp flags. Download and run cPanel’s official ioc_checksessions_files.sh script via SSH root to scan automatically, flagging CRITICAL (confirmed exploit) vs WARNING (suspicious). Purge raw/cache dirs afterward to evict active sessions.
What logs reveal unauthorized access during the exploit window?
Focus on /usr/local/cpanel/logs/access_log for WHM/cPanel login attempts from foreign IPs, /var/log/wtmp via last -a for SSH, and Apache logs for malicious POST/eval() requests, especially Feb 23-Apr 28, 2026. These capture brute-force, session injections, and post-breach activity. Cross-reference with timestamps to spot anomalies like non-local origins.
How do I detect and remove backdoors left by hackers?
Audit WHM API tokens (revoke unknowns), ~/.ssh/authorized_keys for rogue entries, all user crons for wget/curl downloads, PHP files for webshells (e.g., db.php), and processes for XMRig/nuclear.x86 via top. Reset all credentials, delete unauthorized accounts/crons. Use Imunify360 or ClamAV for full scans, then monitor for reappearance.
What immediate steps follow confirming a server hack?
Take the server offline/firewall-block access, purge /var/cpanel/sessions/* and auth/*, reset root/WHM/cPanel/FTP/DB/SSH passwords, revoke API tokens, remove rogue accounts/crons. Run full malware scans and consider OS rebuild from clean backups if root was breached. Harden with 2FA, IP restrictions, CSF, and offsite backups to prevent recurrence.