Linux Server Hacked via cPanel: Data Recovery Guide
Finding out your Linux server was hacked is a nightmare. Your websites go down. Your databases vanish. You might even see a ransom note on your screen. If your Linux server was hacked via a cPanel exploit, you are likely in panic mode right now. But take a deep breath. You have options.
This guide will walk you through the exact steps for Linux server data recovery after a hack. We will look at the recent CVE-2026-41940 exploit. We will explore how to deal with the .sorry ransomware. Most importantly, we will show you how to recover your files, emails, and databases.
We know how stressful this is. Every second counts when you want to recover data after a cPanel hack. Let’s get to work and get your data back safely.
What Happens to Your Data When a Linux cPanel Server Gets Hacked?
A cPanel hacked server file recovery process starts with understanding the attack. When attackers break into your server, they want control. They want your data. Once they get inside, they can do a lot of damage very quickly.
How CVE-2026-41940 Gave Hackers Full Root Access to Every File on the Server
The recent cPanel hack involving CVE-2026-41940 was devastating. It allowed attackers to bypass normal security checks. They gained full root access. With root access, hackers own the server. They can read, modify, or delete every single file. This includes your system files and your customer data. This is why a cPanel WHM root access data theft event is so severe.
What Attackers Typically Do to Data Once Inside — Steal, Encrypt, or Delete
Once hackers get root access, they usually do three things. First, they steal sensitive data. This includes passwords and customer details. Second, they encrypt files to ask for a ransom. Finally, they might just wipe the server completely. If your server was wiped after a cPanel exploit, recovery becomes much harder. They often target the public_html folders first.
The .sorry Ransomware — How the Go-Based Encryptor Locks Linux Server Files
Many victims of this exploit faced the .sorry ransomware. This malware is written in the Go programming language. It is fast and deadly. It uses strong AES encryption to lock your files. When the .sorry ransomware cPanel Linux attack hits, it changes your file extensions to .sorry. It targets databases, website files, and even local backups.
Why Root-Level Access Makes Full Data Recovery Significantly Harder
Root access makes a Linux server compromised data recovery effort very tough. Hackers can delete your backup logs. They can disable your security software. They can even wipe the server logs to hide their tracks. When attackers have root privileges, they can destroy the very tools you need to fix the server.
The Critical Decision — Recovery vs Full Server Rebuild
You must make a choice right now. Do you try to clean the infected server? Or do you wipe it and rebuild from scratch? A full server rebuild from scratch is usually the safest option. Cleaning a hacked server is risky. Hackers often leave hidden backdoors. We highly recommend rebuilding the server and moving your recovered data to a clean OS.
What Is the Very First Thing You Must Do Before Attempting Data Recovery?
Stop right now. Do not start typing random commands. If you make a mistake now, you could lose your data forever. A proper Linux server forensic analysis after a hack requires patience.
Stop All Writes to the Server Immediately — Why Every Second Counts
When a file is deleted, the data is not gone instantly. The system just marks the space as empty. If you write new data to the disk, it will overwrite your deleted files. This makes a cPanel file deleted recovery impossible. You must stop all writes. Turn off web services. Shut down MySQL. Stop incoming emails.
Creating a Full Disk Image or Snapshot Before Any Recovery Attempt
Before you change anything, you need a backup of the hacked state. You need a Linux disk image before recovery begins. If you are on a VPS, take a server snapshot from your hosting panel. This is your safety net. If your recovery steps fail, you can always revert to this cPanel forensic preservation disk image.
Remounting the Filesystem as Read-Only to Preserve Remaining Data
To prevent accidental data overwrites, you should perform a remount read-only Linux recovery step. Run this command: mount -o remount,ro /. This locks the disk. No new data can be written. This gives you time to plan your cPanel public_html files deleted recovery safely.
Why You Must Not Reboot the Server Before Checking for Open File Handles
Do not reboot your server! If you reboot, you clear the system memory. Sometimes, deleted files are still held open by running processes. If you reboot, you lose the chance to use the /proc/PID/fd open file recovery method. We will explain how to use this method later. Keep the server powered on.
Documenting the State of the Server Before Touching Anything
Write everything down. Note what time you noticed the hack. Record which files look encrypted. Copy the ransom note text. Good notes will help you or a professional data recovery Linux server expert later.
Can You Recover Data From cPanel Backups After a Hack?
Backups are your best friend right now. A cPanel clean backup restore point is the easiest way to get your sites back online. But hackers know this too. They often target backups first.
Checking for Existing cPanel Full Backups in /backup Directory
First, check your local backups. Look inside the /backup directory. Check if you have any recent .tar.gz files. Unfortunately, if the hackers had root access, they probably deleted or encrypted these files.
Downloading WHM Full Backups and cpmove Account Files
If you find a surviving cPanel WHM full backup download it immediately to your local computer. Do not leave it on the hacked server. These cpmove files contain your website files, emails, and databases. You can use a cPanel full backup cpmove file to restore an account on a brand new, clean server. Read the official cPanel documentation on backups for exact steps.
Using JetBackup to Restore From Independent Off-Site Backups
If you use JetBackup, you might be in luck. JetBackup often stores data off-site. This means hackers cannot reach it easily. A cPanel backup restore JetBackup process is usually fast. You can restore entire accounts or single files. Check the JetBackup restore guide for detailed instructions. JetBackup independent backup restore is a lifesaver.
Restoring From S3-Compatible Remote Backup Storage
Did you set up Amazon S3 or a similar remote storage? If so, your backups are safe. A cPanel backup remote S3 restore is very secure. The hackers only compromised the server, not your remote storage buckets. Pull these files down to a safe, local environment first.
Identifying a Clean Backup Point Before February 23 2026
If you were hit by the CVE-2026-41940 exploit, you need a cPanel backup before February 23 2026. This was the date the exploit went wild. If you restore a backup from after this date, you might restore the hacker’s backdoors too. Always pick a backup from a known clean date.
What to Do if Attackers Deleted or Encrypted Your Backups
If your local and remote backups are gone, do not panic yet. A cPanel ransomware encrypted file recovery is difficult, but we still have options. We must now look at advanced Linux data recovery tools.
How Do You Recover Deleted Files on a Linux cPanel Server Without Backups?
If you have a cPanel file recovery no backup options scenario, you must dig deep. Linux file systems like ext4 keep track of data in complex ways. We can use specialized tools to find deleted data.
The /proc/PID/fd Method — Recovering Files Still Held Open by Running Processes
Did an attacker delete a file while a program was still using it? If so, the file still exists in memory. You can use the /proc/PID/fd open file recovery trick. Run lsof | grep deleted to see a list. Find the process ID (PID) and the file descriptor number. You can simply copy the file out: cp /proc/PID/fd/5 /safe/location/recovered_file. This is why we told you not to reboot!
Using extundelete to Recover Deleted Files From ext4 Partitions
If the file is fully deleted, try extundelete. This is a powerful extundelete ext4 file recovery Linux tool. It reads the file system journal to find deleted files. Run it on an unmounted or read-only partition. The command extundelete /dev/sda1 --restore-all will attempt to recover everything it can find. You can also try ext4magic deleted file recovery as an alternative tool.
Using debugfs to Access ext4 Internals and Recover by Inode Number
Advanced users can use debugfs. This tool lets you interact directly with the ext4 file system. A debugfs inode recovery Linux process requires you to know the inode number of the deleted file. It is complex, but it works well for a Linux rm -rf recovery situation when the journal is still intact.
Using PhotoRec for Signature-Based File Recovery When Metadata Is Gone
If the file system journal is wiped, metadata is gone. You cannot recover filenames. But you can recover the raw data using PhotoRec. A PhotoRec Linux recovery tool scans the hard drive bit by bit. It looks for file signatures like JPG headers or ZIP headers. It will recover thousands of files with random names. You will have to sort them manually. You can download it from the CGSecurity PhotoRec official site.
Using TestDisk to Recover Lost Partitions and Directory Structures
Did the hackers delete your entire partition? TestDisk server data recovery is your answer. TestDisk can find lost partitions and rewrite the partition table. It can also undelete files from FAT, NTFS, and ext2 filesystems. Find it at the CGSecurity TestDisk official site.
Why XFS Recovery Without Backups Is Largely Unreliable and What to Do Instead
Many modern CentOS and AlmaLinux servers use XFS instead of ext4. Sadly, Linux XFS data recovery limitations are severe. XFS does not keep the same type of journal as ext4. When a file is deleted on XFS, it is usually gone for good. If you run XFS without backups, you will likely need a professional data recovery Linux server service to help you.
How Do You Recover MySQL Databases After a cPanel Server Hack?
Websites need their databases to run. A cPanel MySQL database restore after a hack is a top priority.
Checking for Surviving MySQL Data Files in /var/lib/mysql
Check the /var/lib/mysql directory. Did the hackers delete the raw .ibd and .frm files? If these files are still there, copy them to a safe place immediately. You can often restore a database just from these raw files if you have a clean MySQL server to attach them to.
Recovering MySQL Databases From cPanel Backup Archives
The easiest cPanel database MySQL recovery method is using your .tar.gz backups. Extract the archive. Look for the mysql folder inside. You will find standard .sql files. You can easily import these into a new server.
Using mysqldump and mysqlcheck to Extract and Verify Surviving Databases
If the MySQL service is still running, try to dump the data. Run mysqldump to export all databases to a safe text file. Then, run mysqlcheck to look for corrupted tables. Hackers often corrupt tables while trying to steal data. Always follow MySQL official backup documentation.
Recovering WordPress Databases From wp-content and wp-config.php
If you need a cPanel WordPress database recovery, start with the wp-config.php file. This file holds your database name, username, and password. If the database is gone but you have a SQL dump, use these credentials to reconnect everything on a clean server.
What to Do if MySQL Data Was Encrypted by Ransomware
If the .sorry ransomware encrypted your /var/lib/mysql folder, do not pay the ransom. Check for cPanel hack ransomware decryption tools online first. Security researchers often release free decryption keys weeks after an attack. Until then, rely on your offsite backup recovery.
How Do You Recover cPanel Email Data After a Server Hack?
Emails contain critical business data. A cPanel email data recovery after a breach is vital.
Locating Maildir Files in /home/username/mail/
cPanel stores emails in the Maildir format. You can find these files in /home/username/mail/. Each email is a separate text file. If the hackers did not wipe this directory, your emails are safe. Copy this folder to your local machine right away.
Restoring Email Accounts From WHM Backup Archives
You can perform a cPanel account restore from backup to get your emails back. When you restore a cpmove file, WHM will rebuild the email accounts and put the Maildir files back in place. Need help setting up a secure mail server later? Read our guide on how to set up a VPS mail server.
Recovering Email From Remote IMAP Clients That Cached Messages Locally
What if the server emails are totally gone? Check your phone or computer. Email clients like Outlook or Apple Mail often download local copies. You can export these cached messages and upload them to your new server later.
Rebuilding Email Configuration After a Full Server Rebuild
After a hack, do not copy old email configuration files. They might be compromised. Rebuild your email settings from scratch on the new server. Create the accounts again in cPanel. Then, move the old Maildir files into the new empty folders.
How Do You Recover WordPress and CMS Website Files After a cPanel Hack?
WordPress is a massive target for hackers. They love to inject spam links and malware into WordPress core files.
Restoring WordPress Files From cPanel Full Account Backups
If you have a clean backup, extract your public_html folder. But be careful. If the backup is from after the initial breach, it will contain malware. Always restore your cPanel file manager restore files into a quarantine folder first.
Recovering wp-config.php and Verifying Database Credentials
The most important file is wp-config.php. It connects your site to the database. If you lost this file, you must recreate it. You will need to reset your database passwords in cPanel and update the new wp-config.php file.
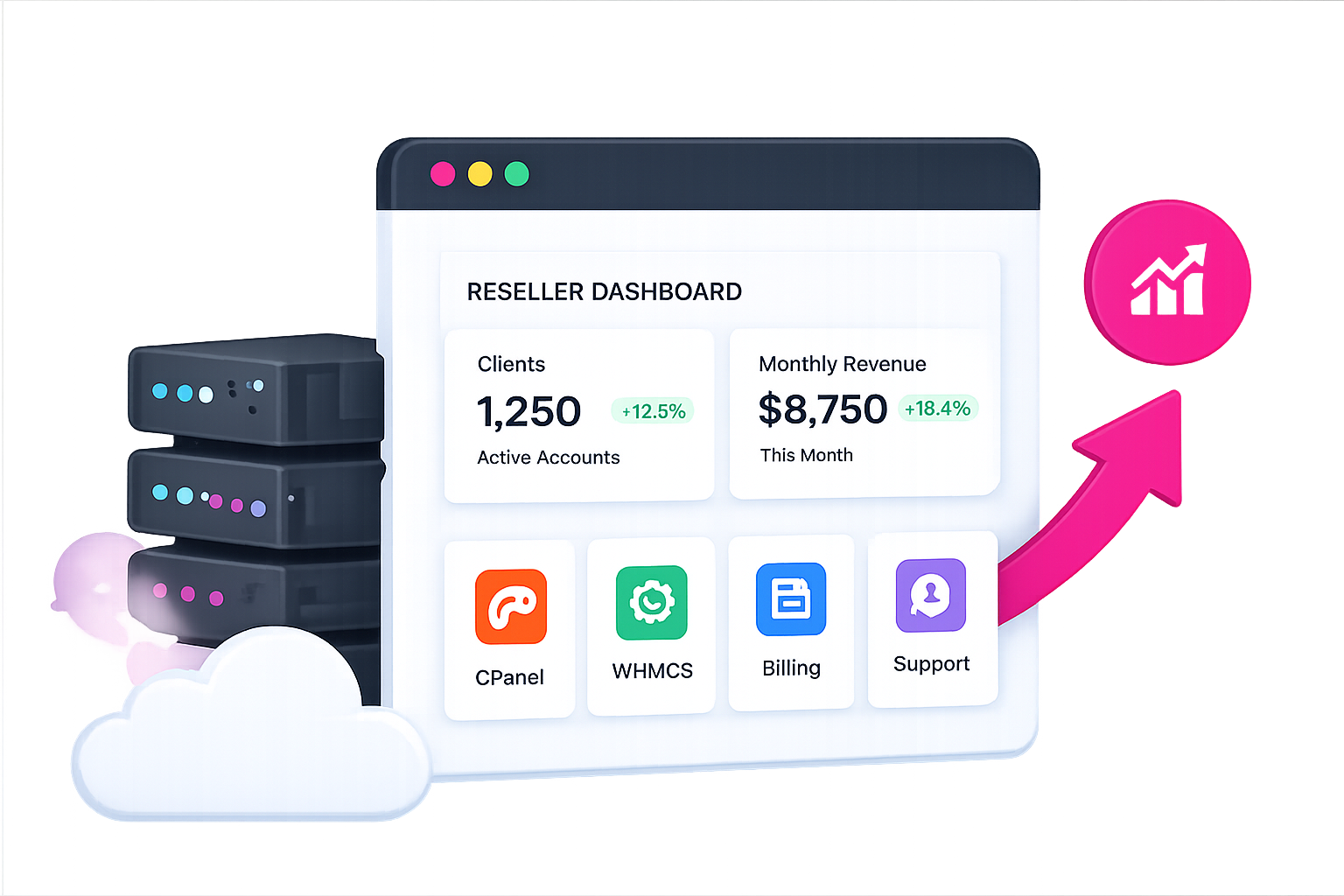
Scanning Restored Files for Malware Before Going Live
Never put recovered files straight onto a live server. Hackers hide backdoors in themes and plugins. Run a malware scanner like Imunify360 or ClamAV on the restored files. If you provide hosting to clients, you should know what reseller hosting includes regarding automated malware scans.
Rebuilding WordPress From a Clean Install and Importing Clean Database
The absolute safest method is a clean rebuild. Install a brand new copy of WordPress. Only copy your wp-content/uploads folder from the hacked server. Reinstall your themes and plugins from the official repositories. Then, import your clean .sql database. Check out WordPress security hardening guides to lock it down.
Checking Cached Versions via Google Cache and Wayback Machine
Did you lose your theme files completely? You can view your site on the Wayback Machine or Google Cache. You can manually copy the text and recreate your pages. It is tedious work, but it saves your content.
How Do You Rebuild a Linux cPanel Server After a Complete Compromise?
You recovered your data. Now you need a safe place to put it. Do not use the hacked server.
When to Choose a Full OS Reload Over a Targeted Cleanup
Always choose a full OS reload. A cPanel clean OS rebuild restore data approach is the only way to guarantee the hackers are gone. Targeted cleanups always miss something. Wipe the drive. Reinstall AlmaLinux or Ubuntu. Install a fresh copy of cPanel.
Step-by-Step Server Rebuild Process After a CVE-2026-41940 Compromise
- Format the server hard drive completely.
- Install a fresh, updated Linux operating system.
- Apply all security patches immediately.
- Install cPanel/WHM.
- Secure the server firewall before restoring data.
If you are moving to a new VPS during this process, read our guide on how to move a site to VPS hosting.
Restoring cPanel Accounts Using pkgacct and Restore Account in WHM
Use the cPanel backup WHM transfer account feature. You can use the pkgacct script to package safe accounts. Then, use the “Restore a Full Backup/cpmove File” tool in WHM to bring the accounts online. This cPanel account pkgacct restore method rebuilds all the necessary system users and permissions safely.
Verifying Restored Data Integrity With Hash Checks Before Going Live
Before you point your DNS to the new server, do a cPanel hash verification after restore. Check that your critical files match the hashes of clean files. Ensure no new malware was introduced during the file transfer.
Security Hardening the Rebuilt Server Before Reactivation
You must harden your new server. Change your SSH port. Use SSH keys instead of passwords. Install a strong firewall like CSF. Enable ModSecurity. If you need a comprehensive checklist, see our VPS management setup guide.
How Do You Prevent Permanent Data Loss on a cPanel Server in the Future?
You survived this hack. You recovered your data. Now, you must make sure you never go through this stress again. A proper backup strategy is your best defense against the next cPanel hack.
Daily Automated Off-Site Backups Independent From the Control Panel
Do not rely solely on cPanel’s built-in backups. If cPanel gets hacked, your backups get deleted. You need a cPanel offsite backup recovery plan. Use tools like JetBackup or R1Soft. Send your data to a remote server that has completely different login credentials.
LVM Snapshots for Fast Point-in-Time Recovery on Linux Servers
If your server uses LVM (Logical Volume Manager), you can take instant snapshots of your disk. A Linux LVM snapshot recovery takes seconds. You can snapshot the server right before a major update. If things go wrong, you roll back instantly.
Setting a 30-Day Backup Retention Policy as a Minimum
Keep your backups for at least 30 days. Sometimes, hackers breach a server but wait weeks before deploying ransomware. If you only keep 7 days of backups, all your backups will contain the hacker’s backdoor. A cPanel incremental backup strategy makes storing 30 days of data affordable.
Testing Backup Restoration Monthly Before a Crisis Occurs
A backup is useless if it does not restore. You must test your cPanel backup restoration SSH process every month. Restore a random account to a test server. Verify the databases connect. Check if the emails load. If you are a web designer managing client sites, regular testing is a great way to earn recurring income while providing massive value.
How SkyNetHosting.Net Protects Client Data and Handles Disaster Recovery
At SkyNetHosting, we take server security seriously. We offer a robust cPanel hosting provider data recovery SLA. We utilize proactive malware scanning and isolated off-site backups. Whether you are running a small blog or looking for scalable VPS hosting for SaaS, we build our infrastructure to withstand attacks.
If you are tired of managing server security yourself, consider upgrading your host. Learn more in our guide on how to choose a secure hosting provider. You handle your business. We will handle the hackers.